Every day, millions of people sign up for digital platforms-marketplaces, gig economy apps, dating sites, and freelance hubs. For most users, this process is a quick hurdle to get to the good stuff. But for human traffickers, these same onboarding screens are gateways to exploitation. They look for weak spots in identity verification (KYC) and safety checks to create fake accounts, recruit victims, or launder money.
The problem isn’t that platforms don’t care. It’s that many still treat onboarding as a friction-reduction exercise rather than a critical defense layer. When you prioritize speed over scrutiny, you leave the door open for bad actors who are highly motivated, tech-savvy, and organized. The good news? You can design onboarding workflows that deter traffickers without alienating legitimate users. It requires shifting from static checks to dynamic, behavioral, and contextual analysis.
Why Traditional KYC Fails Against Traffickers
KYC is the process of verifying a customer's identity to prevent fraud, money laundering, and terrorist financing. In its traditional form, KYC relies heavily on document submission-a driver’s license, passport, or utility bill-and facial recognition matching. This approach works well for stopping casual fraudsters but falls short against sophisticated trafficking networks.
Traffickers often use stolen identities or synthetic identities (combining real and fake data) that pass basic document checks. They might also coerce victims into providing their own biometric data during signup, making the account appear legitimate. A simple selfie match doesn’t reveal coercion, duress, or the presence of a third party controlling the device.
Consider this scenario: A victim is forced to sign up for a gig work app under threat. The trafficker holds the phone, guides the victim through the selfie capture, and ensures the lighting matches the ID photo. The system sees a valid ID and a matching face. It approves the account. The victim is now trapped in an exploitative situation, and the platform has unknowingly facilitated it.
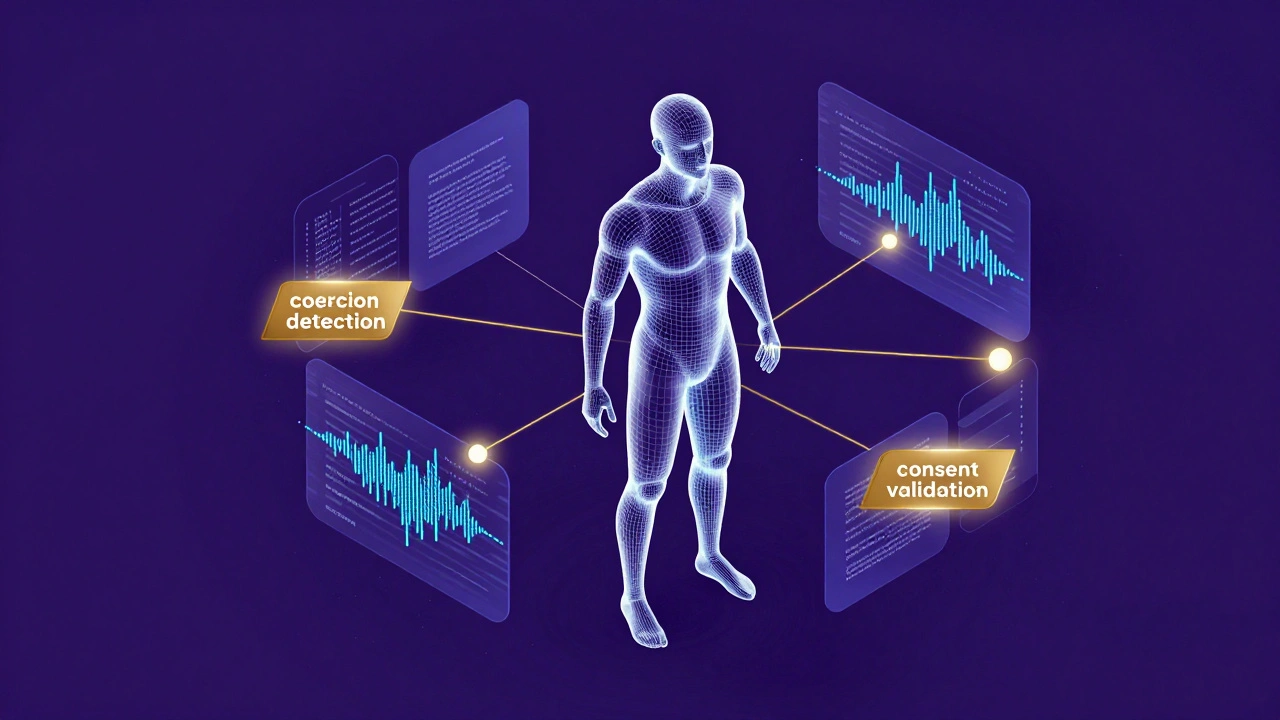
To combat this, platforms need to move beyond “is this person who they say they are?” to “is this person signing up freely and safely?” This shift requires integrating safety checks into the core KYC workflow.
Core Components of Anti-Trafficking Onboarding
An effective onboarding workflow that deters traffickers combines several layers of verification and monitoring. These components work together to create a high-friction environment for bad actors while remaining manageable for genuine users.
- Multi-Factor Identity Verification: Beyond documents, verify ownership of the phone number and email address used. Traffickers often use burner phones or disposable emails. Require SIM swap detection and check if the number has been recently activated or associated with known fraud rings.
- Behavioral Biometrics: Analyze how the user interacts with the onboarding flow. Are they typing naturally? Do they hesitate significantly when asked for personal details? Is someone else guiding them via voice commands? Unusual patterns can flag potential coercion.
- Contextual Risk Assessment: Evaluate the device’s location, IP address, and network environment. If the signup occurs from a data center, VPN, or Tor exit node, apply stricter scrutiny. Cross-reference geolocation with the ID’s issuing region to spot mismatches.
- Consent Validation Mechanisms: Include subtle cues to ensure voluntary participation. For example, ask users to read and acknowledge a safety statement aloud or type a specific phrase. Monitor for signs of distress or hesitation.
- Post-Onboarding Monitoring: Onboarding isn’t a one-time event. Continuously monitor account activity for red flags like sudden changes in location, rapid transaction volumes, or communication patterns indicative of control.
These steps aren’t just about catching criminals; they’re about protecting vulnerable individuals before harm occurs. Each layer adds a bit more friction, but collectively, they make it exponentially harder for traffickers to operate at scale.
Designing Friction Without Alienating Users
The biggest challenge in implementing robust safety checks is balancing security with user experience. Too much friction drives away legitimate users; too little invites abuse. The key is adaptive friction-applying higher scrutiny only when risk indicators are present.
Start with a lightweight baseline for low-risk users. If someone signs up from a trusted device, using a long-standing phone number, in a familiar location, keep the process smooth. But if any anomaly appears-new device, unusual IP, mismatched geolocation-escalate to enhanced verification.
Enhanced verification might include:
- Live video interview with a trained agent who looks for signs of coercion.
- Additional document requests, such as proof of residence or employment.
- Step-up authentication requiring multiple forms of ID.
- Delayed approval pending manual review.
This tiered approach ensures that 95% of users experience minimal disruption while the remaining 5%-those triggering risk signals-are subjected to deeper scrutiny. It’s efficient, scalable, and focused where it matters most.
Transparency also helps. Explain why certain checks are necessary. Users are more willing to comply when they understand the purpose. Phrases like “We verify your identity to protect you and our community” resonate better than opaque demands.
Technology Tools for Enhanced Detection
Modern platforms have access to powerful tools that can automate much of the anti-trafficking detection process. Leveraging these technologies reduces reliance on manual reviews and improves accuracy.
| Tool Type | Function | Effectiveness Against Trafficking | User Impact |
|---|---|---|---|
| Biometric Liveness Detection | Ensures the person presenting the ID is physically present and not using a photo or mask. | High - prevents spoofing and deepfake attacks. | Low - quick selfie-based check. |
| Device Fingerprinting | Identifies unique hardware characteristics of the device used for signup. | Medium - detects reused devices across multiple fraudulent accounts. | Negligible - runs in background. |
| AI Behavioral Analysis | Analyzes keystroke dynamics, mouse movements, and interaction patterns. | High - identifies coercion or remote control attempts. | Low - no additional user action required. |
| Geolocation Intelligence | Verifies physical location against IP address and GPS data. | Medium - flags inconsistencies between claimed and actual location. | Low - may require permission prompts. |
| Social Graph Mapping | Maps connections between users to identify coordinated fraud networks. | Very High - uncovers organized trafficking rings. | None - operates post-onboarding. |
Integrating these tools creates a multi-dimensional view of each user. No single tool is foolproof, but together, they form a robust defense system. Platforms should prioritize those that offer passive monitoring (like device fingerprinting and AI behavioral analysis) since they impose zero extra burden on users.
Legal and Ethical Considerations
Implementing strict onboarding checks raises important legal and ethical questions. Privacy laws like GDPR in Europe and CCPA in California regulate how personal data can be collected, stored, and processed. Over-collection or misuse of sensitive information can lead to severe penalties and reputational damage.
Platforms must adopt a privacy-by-design approach. Collect only what’s necessary for verification and safety. Anonymize data wherever possible. Provide clear opt-out mechanisms for non-essential features. Regularly audit data practices to ensure compliance.
Ethically, there’s a duty to protect vulnerable users without stigmatizing them. Avoid language or processes that could inadvertently target marginalized groups. Ensure that safety checks are applied uniformly and fairly. Train staff involved in manual reviews to recognize signs of trauma and refer them to appropriate resources.
Collaboration with NGOs, law enforcement, and industry bodies strengthens efforts. Sharing anonymized threat intelligence helps everyone stay ahead of emerging tactics. Initiatives like the Global Alliance Against Traffic in Women (GAATW) provide valuable frameworks for ethical implementation.
Building a Culture of Vigilance
Technology alone won’t solve trafficking. It requires a cultural shift within organizations. Employees at all levels-from customer support to engineering-need training to recognize red flags. Create easy reporting channels for both internal staff and external users.
Encourage a speak-up culture. If a support agent notices something odd during a call, they should feel empowered to escalate it. Reward teams that contribute to safety improvements, not just growth metrics.
Partner with experts. Bring in specialists in human trafficking prevention to advise on policy and product design. Their insights can uncover blind spots that internal teams might miss.
Finally, measure success not just by reduction in fraudulent accounts, but by positive outcomes for victims. Track how many cases were identified early, how many referrals were made to support services, and how many survivors reported feeling protected by platform safeguards.
What is KYC and why is it important for preventing trafficking?
KYC stands for Know Your Customer, a process used to verify the identity of individuals before allowing them to use a service. It’s crucial for preventing trafficking because it helps ensure that accounts are created by real, consenting adults rather than traffickers using stolen or synthetic identities. Strong KYC acts as a first line of defense against exploitation.
How can platforms detect coercion during onboarding?
Platforms can detect coercion through behavioral biometrics, which analyze how users interact with the interface. Signs include unusual hesitation, erratic typing patterns, or evidence of remote guidance (e.g., voice commands). Live video interviews with trained agents can also help identify signs of distress or lack of autonomy.
Is it legal to collect biometric data for safety checks?
Yes, but it depends on local regulations. In regions like the EU and California, explicit consent is required, and data must be handled according to strict privacy laws. Platforms should implement privacy-by-design principles, collecting only essential data and ensuring transparency about its use. Always consult legal counsel to ensure compliance.
What role does AI play in anti-trafficking onboarding?
AI plays a significant role by analyzing large datasets for patterns that humans might miss. Machine learning models can detect anomalies in behavior, flag suspicious devices, and map social graphs to uncover coordinated fraud networks. However, AI should complement-not replace-human judgment, especially in sensitive situations involving potential victims.
How do I balance security with user experience?
Use adaptive friction: apply lighter checks to low-risk users and reserve intensive verification for those triggering risk indicators. Be transparent about why certain steps are needed. Test different flows to find the sweet spot where security doesn’t significantly increase drop-off rates among legitimate users.