Consent verification is the process of confirming that performers are adults and have freely agreed to participate in specific sexual acts without coercion. In the adult entertainment industry, this isn't just a legal checkbox; it's the primary defense against human trafficking and exploitation. For producers, platforms, and performers alike, the challenge lies in proving consent without exposing sensitive personal data to hackers or public scrutiny.
The stakes couldn't be higher. In 2024, the U.S. Department of Justice reported a significant rise in online sex trafficking cases linked to inadequate verification protocols on streaming platforms. At the same time, privacy advocates warn that storing government IDs creates massive honeypots for identity theft. So, how do we verify someone is who they say they are-and that they want to be there-without handing over their entire life story to a database?
The Legal Landscape: Beyond 2257 Compliance
Most people know about 18 U.S.C. § 2257, a federal law requiring record-keeping of performers' ages and identities in sexually explicit materials. It’s the baseline. But simply keeping a copy of a driver’s license in a filing cabinet (or a cloud server) doesn’t cut it anymore. Modern compliance requires active verification, not passive storage.
In the European Union, the Digital Services Act (DSA), regulation imposing strict liability on online platforms regarding illegal content has pushed companies toward more robust age assurance systems. Meanwhile, California’s AB 2261 mandates that online platforms implement "reasonable" steps to prevent child sexual abuse material (CSAM). The trend is clear: regulators want proof of age and consent, but they don’t want your raw biometric data sitting in a server farm.
This creates a tension. You need to verify identity to prevent trafficking, but you need to protect privacy to prevent data breaches. The solution isn't choosing one over the other-it's using technology that does both simultaneously.
Zero-Knowledge Proofs: Verifying Without Revealing
One of the most promising tools in this space is Zero-Knowledge Proof (ZKP), a cryptographic method allowing one party to prove a statement is true without revealing any information beyond the validity of the statement itself. Think of it like a bouncer at a club. They need to know you’re over 21, but they don’t need to know your home address, your mother’s maiden name, or your social security number.
With ZKPs, a performer can prove they are over 18 and have signed a consent form for a specific scene without ever uploading their passport photo to the production company’s server. The math proves the facts; the data stays with the user. This is crucial for privacy-safe verification because if the production company gets hacked, there’s nothing to steal. No names, no faces, no dates of birth-just a mathematical confirmation that the requirements were met.
Several startups are already building ZKP-based identity layers specifically for high-risk industries. These systems allow performers to hold their own credentials in a digital wallet. When they join a set, they present a token that says, "I am verified," rather than handing over their ID card.
Biometric Authentication vs. Privacy Risks
Facial recognition and fingerprint scanning are common in banking apps, so why not in adult productions? The short answer: risk. Biometric data is immutable. If your password is stolen, you change it. If your face scan is leaked, you can’t change your face.
However, Live biometric verification, real-time analysis of facial features to confirm identity during a session can play a role if done correctly. Instead of storing static photos, some platforms use live liveness detection. This ensures the person signing the contract is physically present and consenting at that moment, reducing the risk of coerced signings where a trafficker forces a victim to sign under duress off-camera.
To make this privacy-safe, the biometric data should be processed locally on the device and never stored centrally. The system generates a hash-a unique string of characters-that confirms the match. This hash can be used to audit consent records without exposing the actual video or image of the performer.
| Method | Privacy Risk | Anti-Trafficking Efficacy | Cost |
|---|---|---|---|
| Document Upload (ID/Passport) | High (Data Breach) | Medium (Can be forged) | Low |
| Third-Party KYC Providers | Medium (Shared Data) | High (Professional Verification) | Medium |
| Zero-Knowledge Proofs | Very Low (No Data Stored) | High (Cryptographic Certainty) | High (Implementation Cost) |
| Live Biometric Liveness | Medium (If Stored Centrally) | Very High (Real-Time Presence) | Medium |

The Role of Third-Party Auditors
You can’t always trust the house to play fair. Independent auditors are essential for maintaining integrity in the industry. Organizations like VerificationNow, a service provider specializing in age and identity verification for adult content creators act as neutral intermediaries. They verify the performer’s identity and consent status, then issue a digital certificate to the platform.
This model shifts the liability. If a trafficking ring infiltrates a platform, the platform can demonstrate due diligence by showing they relied on a reputable third-party verifier. For performers, it means they don’t have to share their ID with every single website they upload to. They verify once with the trusted auditor, and that credential is recognized across multiple compliant platforms.
These auditors also look for red flags that automated systems miss. Is the performer speaking naturally? Do they seem distracted or monitored by another person? Human oversight remains a critical layer in preventing coercion.
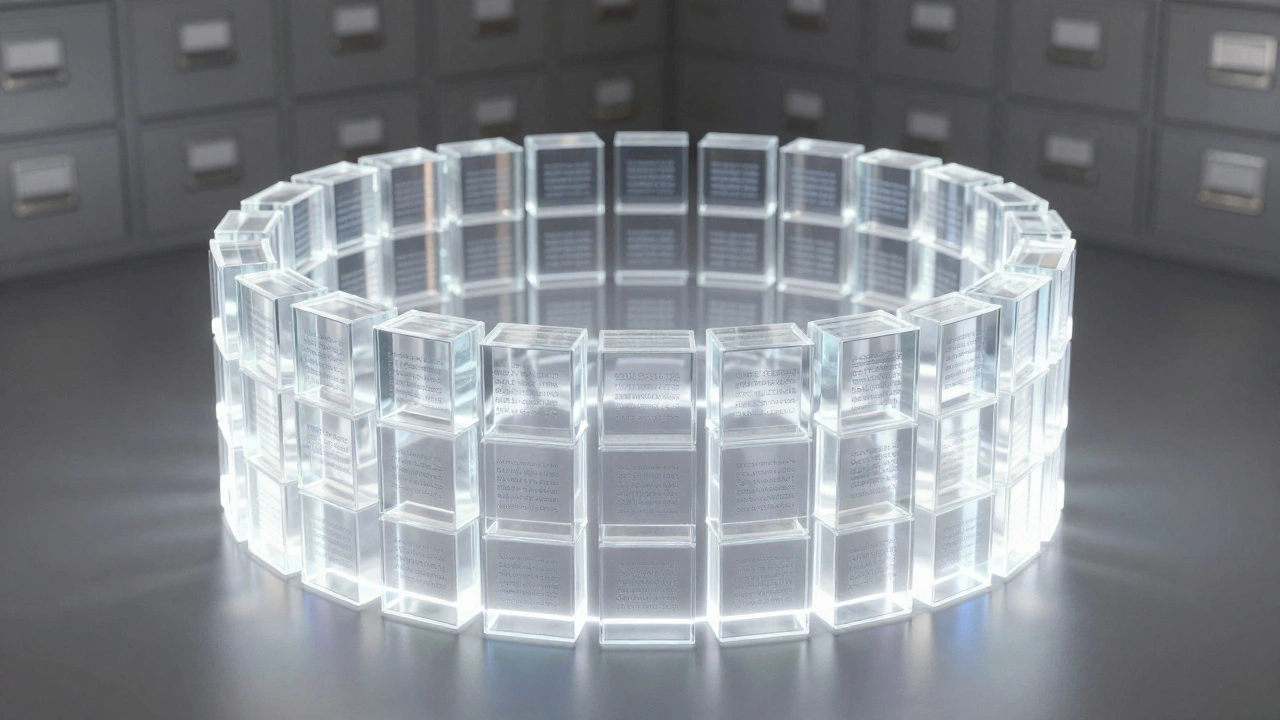
Blockchain for Immutable Consent Records
Consent isn't a one-time event; it's ongoing. A performer might agree to shoot Scene A but refuse Scene B. Traditional databases can be altered, deleted, or lost. Blockchain technology, a decentralized ledger that records transactions securely and transparently offers a way to create an immutable record of consent.
Imagine a smart contract that logs each instance of consent. When a performer agrees to a new scene, a transaction is recorded on the blockchain. This record is timestamped and cannot be changed retroactively. If a dispute arises years later, the blockchain provides undeniable proof of what was agreed upon and when.
Crucially, this doesn't mean putting private details on a public ledger. The blockchain stores hashes of the consent documents. The actual documents remain encrypted and accessible only to authorized parties (the performer, the producer, and perhaps a legal auditor). This ensures transparency without sacrificing confidentiality.
Red Flags: Identifying Coercion and Trafficking
Technology helps, but human intuition still matters. Producers and directors must be trained to spot signs of trafficking. Even with perfect verification tech, a coerced performer might still show up if forced.
- Lack of Control: Does the performer control their own schedule and finances? Or does a manager handle everything?
- Inconsistent Stories: Are there discrepancies in their background or history?
- Fearful Demeanor: Is the performer overly anxious, checking their phone constantly, or unable to leave the set alone?
- Pressure Tactics: Is there someone standing close by during negotiations?
If you see these signs, stop production immediately. Report it to local authorities and organizations like the National Human Trafficking Hotline, a US-based resource providing support and reporting mechanisms for trafficking victims. Privacy-safe verification includes protecting the victim from further harm by not escalating the situation prematurely.
Best Practices for Production Companies
Implementing privacy-safe consent verification requires a shift in mindset. It’s not just about avoiding fines; it’s about ethical responsibility. Here’s how to get started:
- Minimize Data Collection: Only collect what is legally required. Don’t ask for utility bills if a driver’s license suffices.
- Use Encryption: All data must be encrypted at rest and in transit. Use AES-256 standard encryption.
- Regular Audits: Hire independent firms to test your security and verify your processes annually.
- Train Staff: Ensure everyone on set knows how to spot coercion and understands the importance of consent.
- Adopt Emerging Tech: Pilot ZKP solutions or blockchain-ledger systems to future-proof your operations.
The goal is to create an environment where performers feel safe, producers stay compliant, and predators find no foothold. By combining strong cryptography with human vigilance, the industry can move forward without leaving anyone behind.
What is the difference between age verification and consent verification?
Age verification confirms that a person is over the legal age limit (usually 18). Consent verification goes further, ensuring that the individual has freely agreed to participate in specific activities without coercion, force, or fraud. Both are required for legal compliance, but consent verification addresses the risk of trafficking and exploitation directly.
How do Zero-Knowledge Proofs protect performer privacy?
Zero-Knowledge Proofs allow a performer to prove they meet certain criteria (like being over 18) without revealing their actual identity documents. The mathematical proof confirms the fact, but the underlying data (name, photo, ID number) never leaves the performer’s device, making it impossible for hackers to steal personal information from the production company’s servers.
Is blockchain necessary for consent records?
It is not strictly necessary, but it is highly recommended for long-term integrity. Blockchain creates an immutable, timestamped record that cannot be altered or deleted. This prevents disputes over whether consent was given and protects against tampering by malicious insiders or external attackers.
What should I do if I suspect trafficking on set?
Stop production immediately. Do not confront the suspected trafficker directly, as this could endanger the victim. Contact local law enforcement and the National Human Trafficking Hotline (in the US) or equivalent local resources. Document your observations discreetly and preserve any relevant evidence.
Are third-party verification services reliable?
Reputable third-party services are generally more reliable than in-house methods because they specialize in identity verification and anti-fraud measures. They undergo regular audits and use advanced technology to detect forged documents and deepfakes. However, it is important to choose providers that prioritize data privacy and comply with regulations like GDPR and CCPA.
